Capture VM traffic before Firewall rules are applied
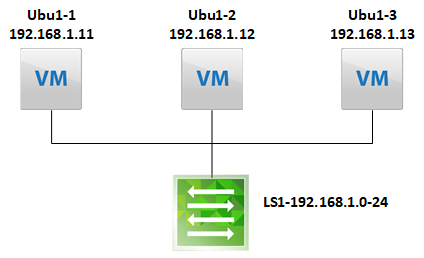
To demonstrate this, I’m going to use a very simple setup, where I’ve configured a dfw rule to block any ICMP related traffic from eth0 of “Ubu1-1”.
Technically, we capture the traffic at the virtual Switch port, so we need to identify the Port Number of the VM NIC.
To do this, we have to ssh to the host, which is hosting the VM in question and run the following command:
[root@esxi2:~] net-stats -l PortNum Type SubType SwitchName MACAddress ClientName 50331650 4 0 DvsPortset-0 54:b2:03:10:b7:46 vmnic0 50331652 3 0 DvsPortset-0 54:b2:03:10:b7:46 vmk0 50331653 3 0 DvsPortset-0 00:50:56:6e:69:57 vmk1 50331654 3 0 DvsPortset-0 00:50:56:6a:b3:36 vmk2 50331655 3 0 DvsPortset-0 00:50:56:64:46:61 vmk3 50331657 5 9 DvsPortset-0 00:50:56:8c:5b:51 ubu1-1.eth0 50331658 5 9 DvsPortset-0 00:50:56:8c:a4:84 ubu1-2.eth0
In line 8, we can see that the Port Number is 50331657.
Next, we start capturing the traffic on the switchport:
[root@esxi2:~] pktcap-uw --switchport 50331657 --dir 0 --stage 0 -o - | tcpdump-uw -enr - icmp
The most important part here is the “- -stage 0”, this defines where the traffic is captured. “0” means, while entering the virtual Switch, which means, immediately after leaving the VM (thus, before firewall rules are applied).
“1” one means, after exiting the virtual Switch (thus, after the packages were processed by the firewall rules).
The pipe to tcpdump is only for a better ability to filter the traffic.
Let’s start a ping on the VM and compare the traffic captures while entering and exiting the virtual switch.
Traffic while entering the virtual Switch:
[root@esxi2:~] pktcap-uw --switchport 50331657 --dir 0 --stage 0 -o - | tcpdump-uw -enr - icmp The switch port id is 0x03000009. The Stage is Pre. pktcap: The output file is -. pktcap: No server port specifed, select 16438 as the port. pktcap: Local CID 2. pktcap: Listen on port 16438. pktcap: Accept...reading from file -, link-type EN10MB (Ethernet) pktcap: Vsock connection from port 1035 cid 2. 22:20:35.420219 00:50:56:8c:5b:51 > 00:50:56:8c:a4:84, ethertype IPv4 (0x0800), length 98: 192.168.1.11 > 192.168.1.12: ICMP echo request, id 1360, seq 1, length 64 22:20:36.424641 00:50:56:8c:5b:51 > 00:50:56:8c:a4:84, ethertype IPv4 (0x0800), length 98: 192.168.1.11 > 192.168.1.12: ICMP echo request, id 1360, seq 2, length 64 22:20:37.448621 00:50:56:8c:5b:51 > 00:50:56:8c:a4:84, ethertype IPv4 (0x0800), length 98: 192.168.1.11 > 192.168.1.12: ICMP echo request, id 1360, seq 3, length 64 22:20:38.472571 00:50:56:8c:5b:51 > 00:50:56:8c:a4:84, ethertype IPv4 (0x0800), length 98: 192.168.1.11 > 192.168.1.12: ICMP echo request, id 1360, seq 4, length 64
Traffic after leaving the virtual Switch:
[root@esxi2:~] pktcap-uw --switchport 50331657 --dir 0 --stage 1 -o - | tcpdump-uw -enr - icmp The switch port id is 0x03000009. The Stage is Post. pktcap: The output file is -. pktcap: No server port specifed, select 13322 as the port. pktcap: Local CID 2. pktcap: Listen on port 13322. reading from file -, link-type EN10MB (Ethernet) pktcap: Accept... pktcap: Vsock connection from port 1034 cid 2.
As you can see, the traffic does not exit the virtual switch.
Just to be sure, check the dfw logs:
[root@esxi2:~] tail -n4 /var/log/dfwpktlogs.log 2019-08-08T22:20:36.424Z 15526 INET match DROP domain-c85/1005 OUT 84 ICMP 192.168.1.11->192.168.1.12 2019-08-08T22:20:37.448Z 15526 INET match DROP domain-c85/1005 OUT 84 ICMP 192.168.1.11->192.168.1.12 2019-08-08T22:20:38.472Z 15526 INET match DROP domain-c85/1005 OUT 84 ICMP 192.168.1.11->192.168.1.12 2019-08-08T22:20:39.496Z 15526 INET match DROP domain-c85/1005 OUT 84 ICMP 192.168.1.11->192.168.1.12
The firewall logs confirm, that the traffic was dropped in between the two capturing points.
Additional Information:
Command Syntax for pktcap-uw
Since vSphere 6.7, you can capture traffic in both directions simultaneously (in earlier versions you had to choose one):
--dir <0|input|1|output|2|inputAndOutput> (for --switchport, --vmk, --uplink, --fcport)
The direction of flow, with respect to the vswitch:
0- Input: to vswitch (Default), 1- Output: from vswitch, 2- Input and Output